Security Posture
How ValkenRoot is being secured
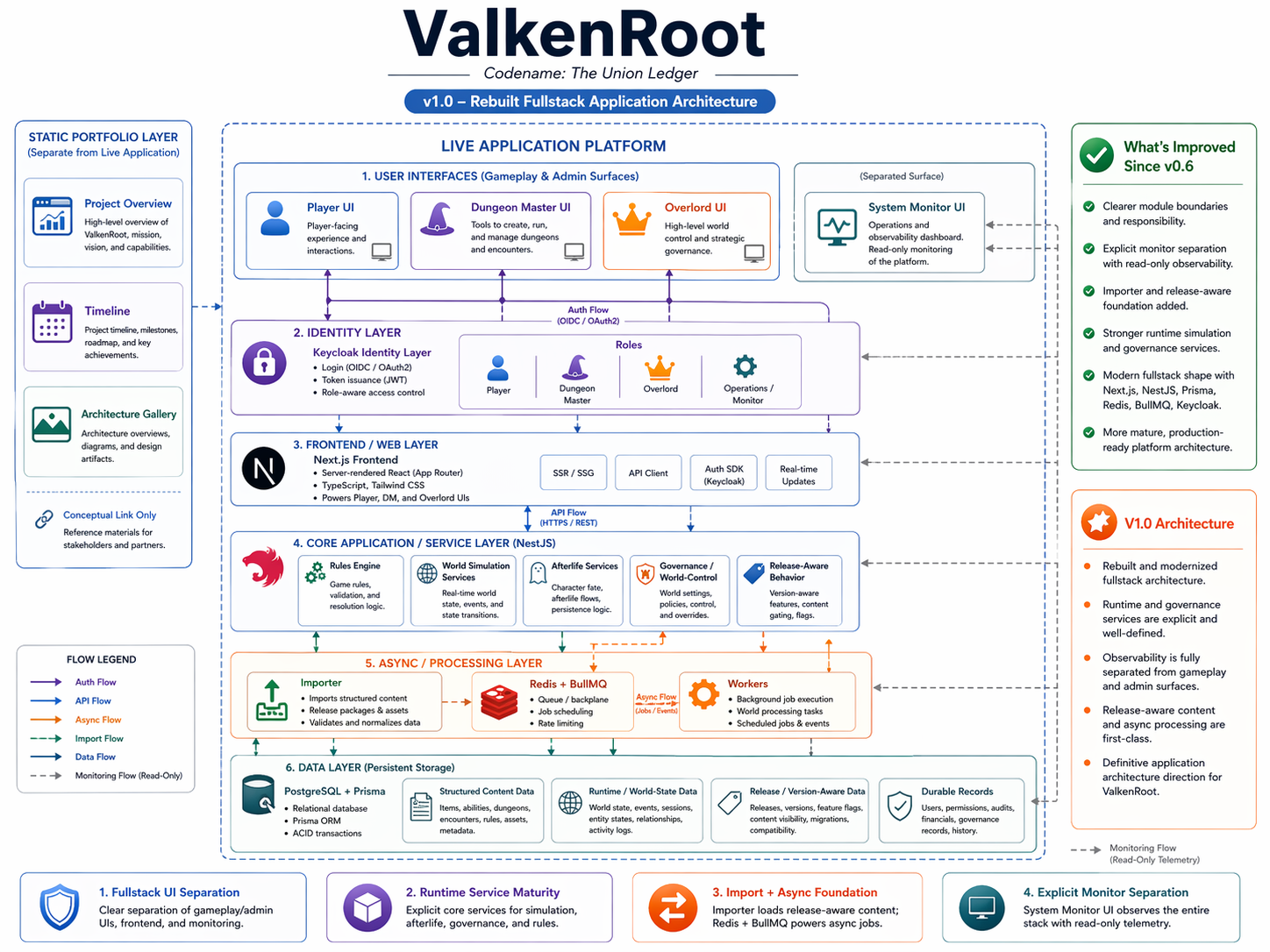
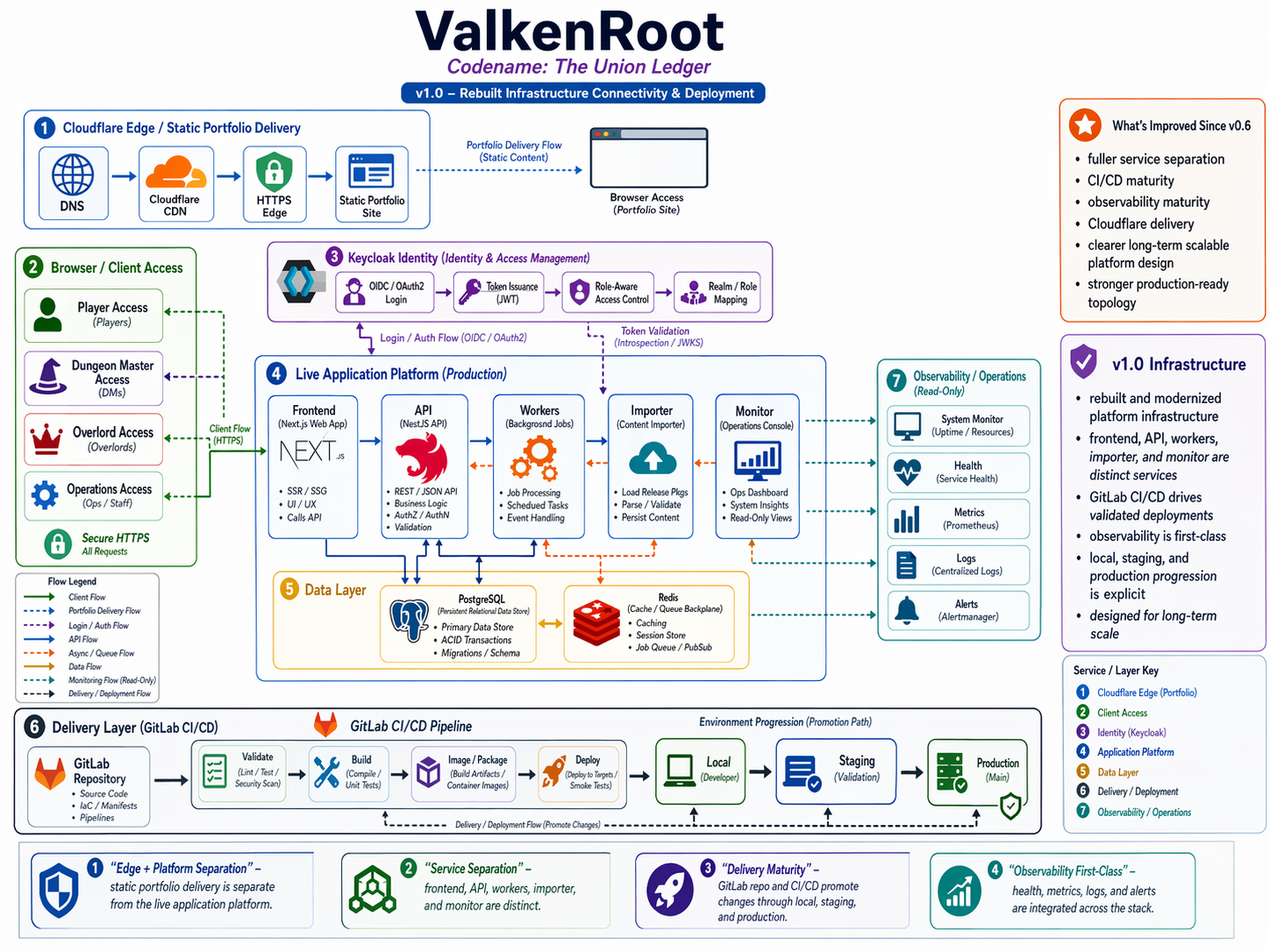
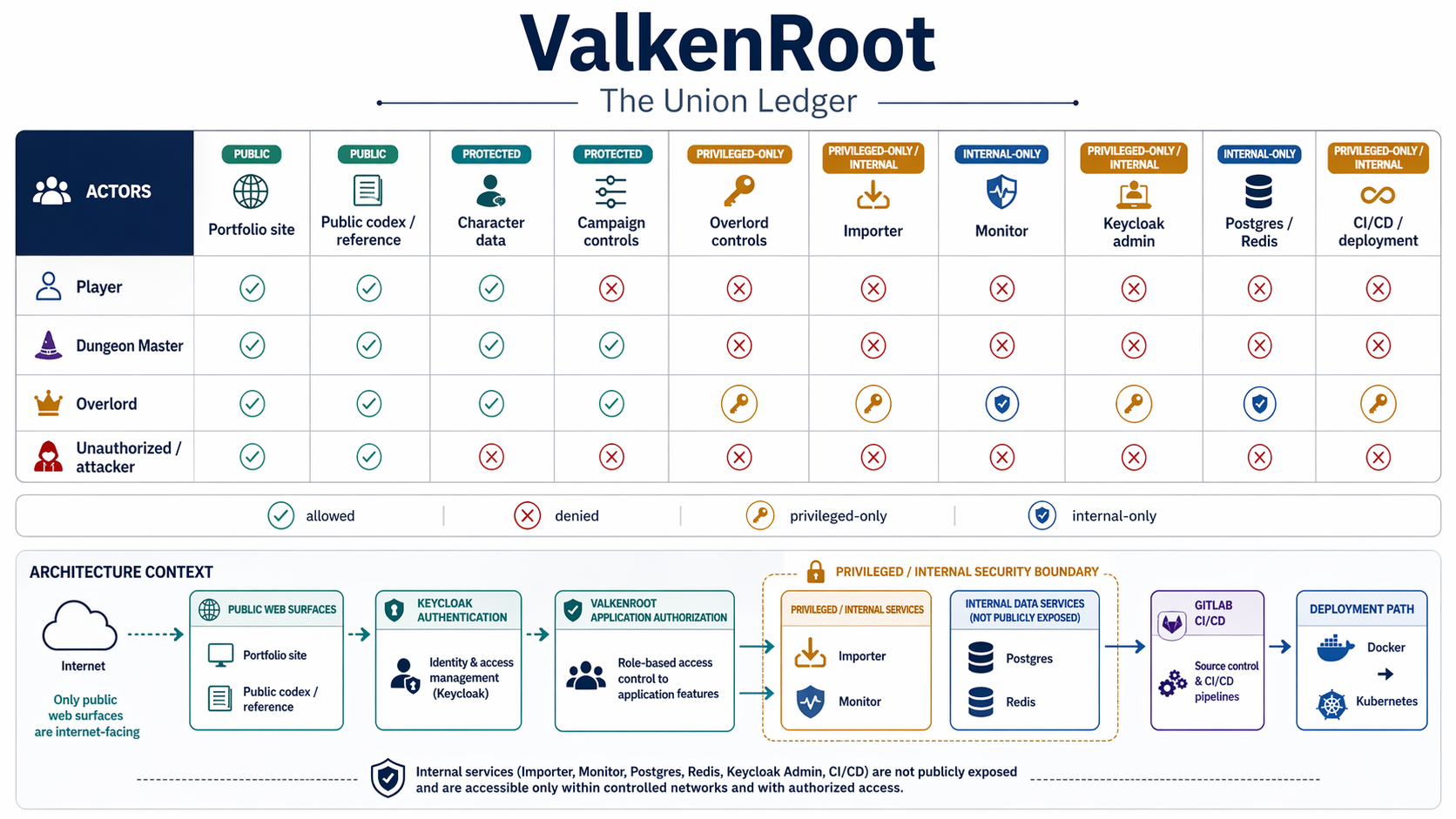
V1.0 security is being shaped around role separation, protected delivery, private
internal services, and stronger resistance to hostile access. The security model is
being built as part of the platform architecture so that gameplay, governance,
deployment, and monitoring evolve with clearer boundaries from the start.
Why security belongs in the portfolio
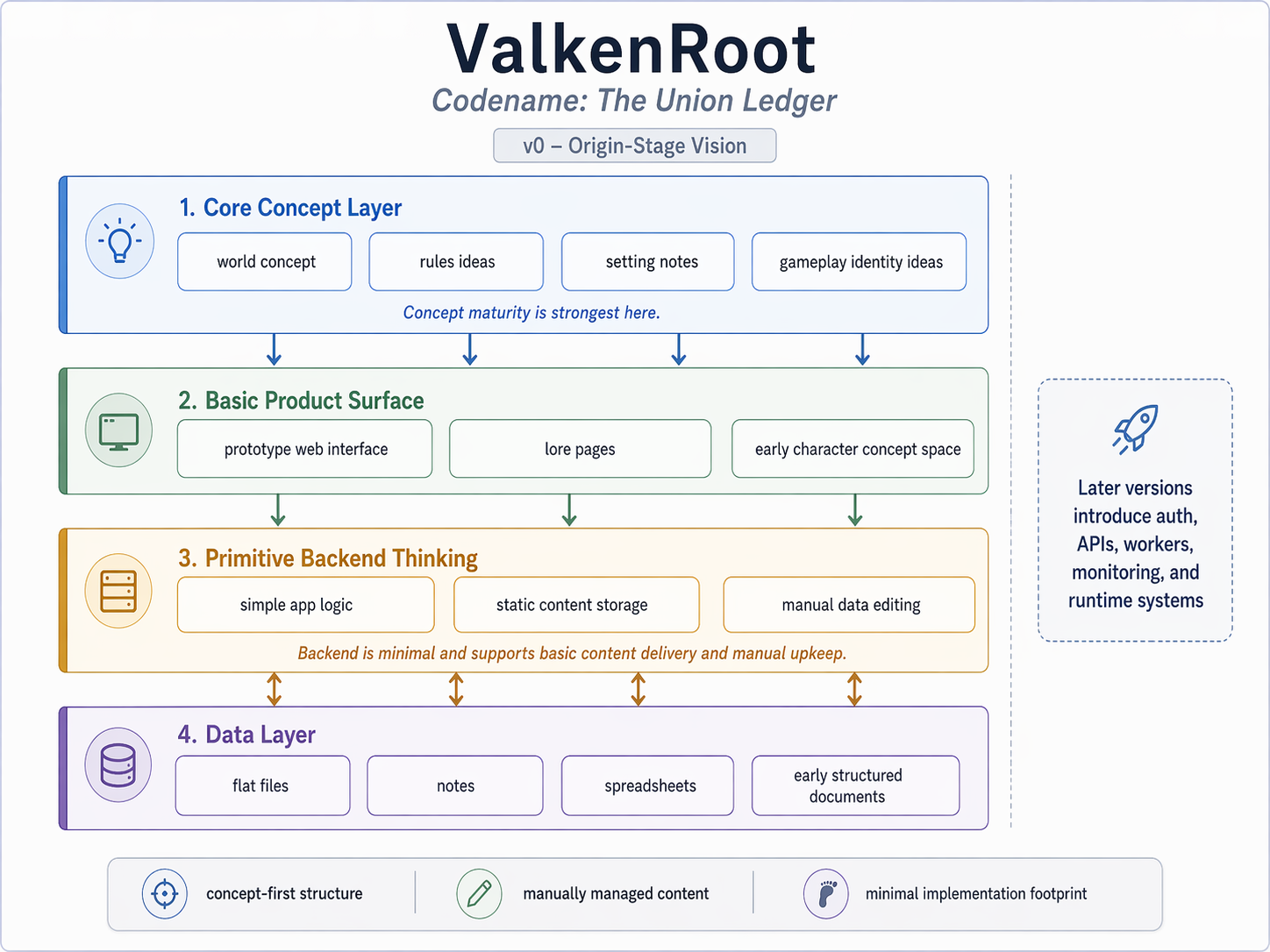
By V1.0, ValkenRoot is no longer only a game concept or a content-heavy design
exercise. It is becoming a real application platform with multiple user types,
privileged roles, protected data, CI/CD delivery, and internal operational surfaces.
That makes security part of the architecture story rather than a separate later
concern.
This section shows how the project is being shaped to withstand misuse, privilege
abuse, and hostile access while still preserving the intended Player, Dungeon
Master, and Overlord workflows.
What this section is showing
- How role-based access is separated across player, campaign, world, and operations surfaces
- How the current V1.0 design compares against major security frameworks
- Where the project is already strong in security intent
- Where practical implementation gaps still exist
- How the hardening path moves from the current baseline toward safer staging and launch
Player
Players should be able to reach their own account, character, progression,
campaign-linked gameplay surfaces, and approved public reference content.
They must not be able to reach importer tooling, Overlord governance, monitor
administration, unrelated campaign data, or infrastructure-facing controls.
This boundary matters because player access is the most numerous and most exposed
surface in the system. If it is not tightly scoped, normal gameplay identity can
become an entry point into privileged platform behavior.
Dungeon Master
Dungeon Masters should be able to manage the campaigns they control, inspect
campaign-linked characters, and operate encounter or campaign-specific tools.
They must not receive global world-governance powers, unrestricted importer access,
or direct control over broader platform operations.
The key security design choice is that DM authority is campaign-scoped rather than
global. A Dungeon Master is powerful inside the campaigns they run, but that should
never collapse into system-wide administrative authority.
Overlord
Overlord is treated as a privileged application role with authority over world
governance, release-aware content direction, and high-level intervention surfaces.
Even then, Overlord should not automatically imply infrastructure administration,
unrestricted CI/CD access, or direct database control without separate operational
privileges.
This separation is deliberate. Overlord is the highest application-governance role,
but it is still not meant to be a blanket superuser over hosting, secrets, data
stores, or deployment systems.
Unauthorized / attacker
Attackers are assumed to probe public APIs, replay tokens, enumerate identifiers,
abuse privileged endpoints, and look for weak staging or default credentials.
The response is deny-by-default access, stronger edge filtering, rate limiting,
private service networking, and enough telemetry to expose abuse early.
This card makes the threat model explicit: ValkenRoot assumes public-facing surfaces
will be probed, so the framework is being shaped to resist enumeration, privilege
escalation, and staging mistakes rather than trusting that those things will not
happen.
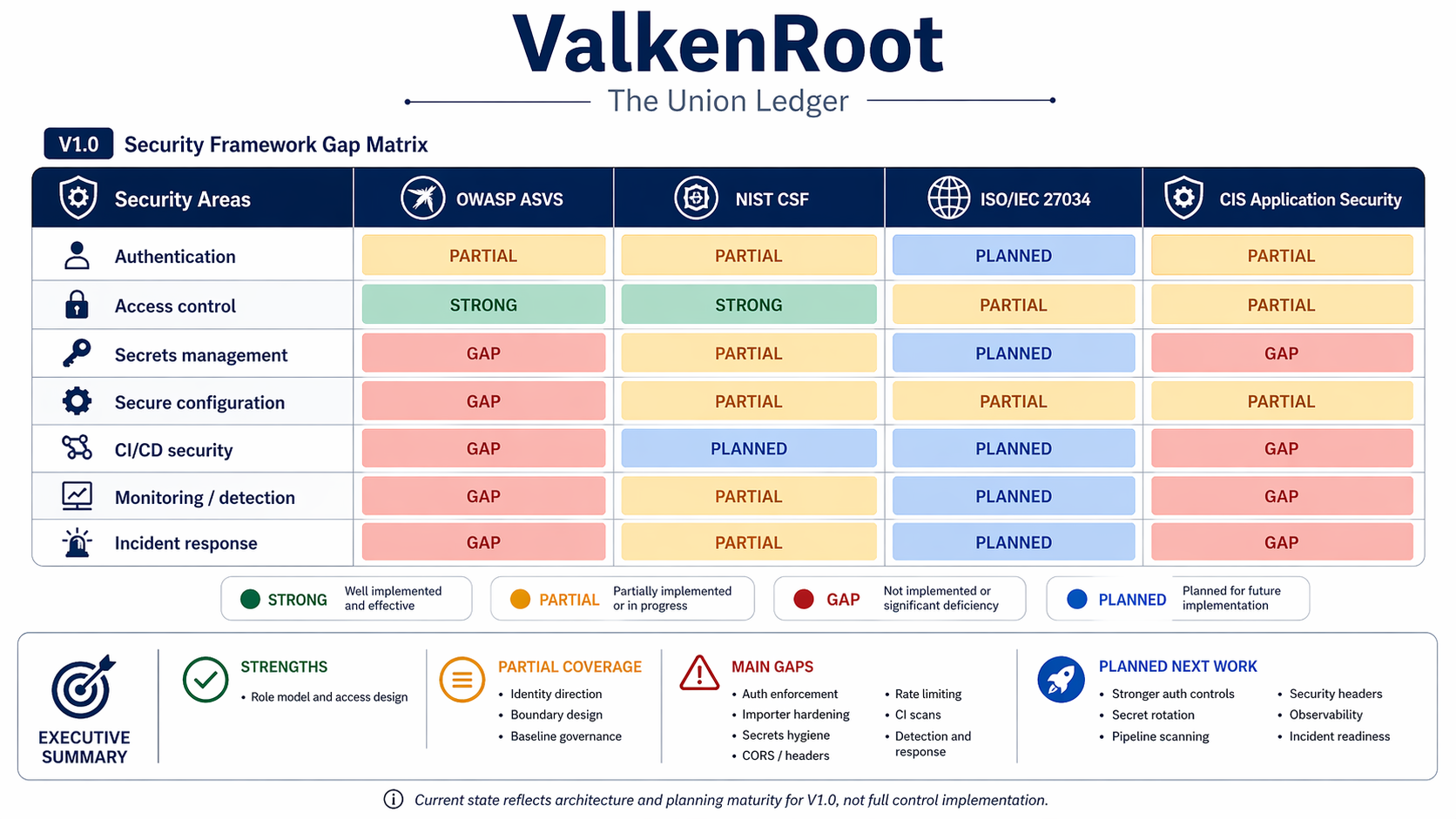
OWASP ASVS
The current design is strongest in role modeling, identity direction, and planned
control boundaries.
It is still immature in applied controls such as strict CORS, route-level auth
enforcement, hardened validation defaults, rate limiting, and importer protection.
In portfolio terms, this means the project already understands what needs to be
protected, but some of the live defensive controls still need to be fully enforced
in code and deployment.
NIST CSF
ValkenRoot already has a good architectural understanding of assets, actors, and
operational surfaces.
The main gaps are in Protect, Detect, Respond, and Recover: security controls,
abuse detection, response playbooks, and restore-tested recovery are not yet fully
implemented.
The strongest current position is in Identify, because actors, services, and system
roles are already being mapped clearly. The weaker areas are the operational
disciplines that must come with an exposed or semi-exposed platform.
ISO/IEC 27034
The project is strong in planning and secure-by-design intent across the software
lifecycle.
It still needs security to become a real SDLC gate through CI checks, environment
separation, release controls, and operational policy enforcement.
This is an important distinction for V1.0: the planning is secure-by-design in
intent, but the secure development lifecycle still has to be turned into concrete
engineering rules and deployment gates.
CIS application security
The architecture is ready for practical hardening through configuration baselines,
secrets discipline, and vulnerability management.
The biggest missing pieces are dependency scanning, secure configuration baselines,
and stronger handling of credentials, internal service exposure, and monitoring.
This is the most practical hardening lens for the current stage because it translates
architecture into service baselines, vulnerability management, and safer defaults
that can actually be enforced during delivery.
Top security gaps right now
- Route-level authentication and authorization enforcement
- Importer protection and privileged route lock-down
- Secret hygiene and removal of weak or default credentials
- CORS, headers, and request hardening at the API edge
- Rate limiting and abuse protection
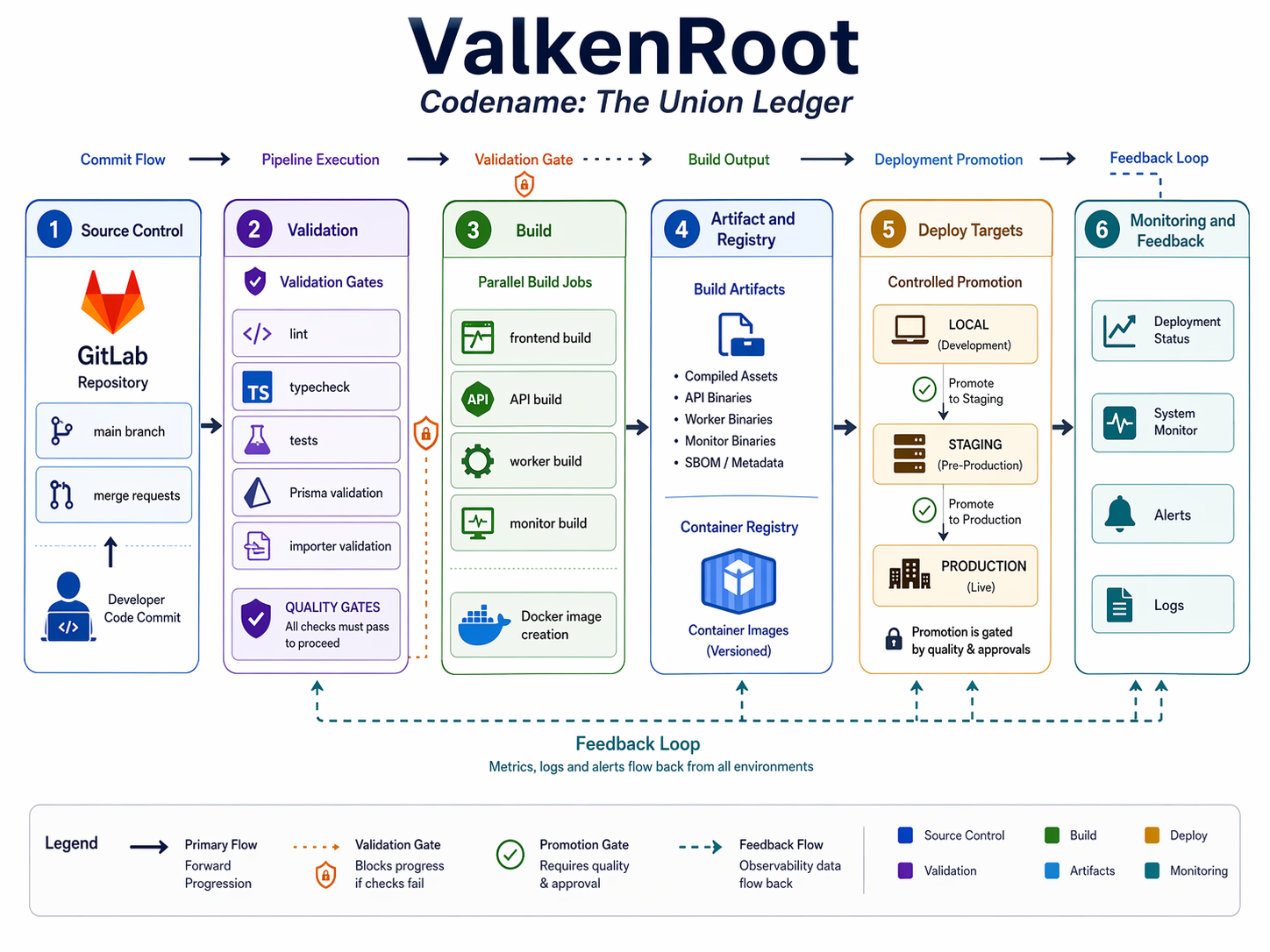
- CI security scanning and deployment safety gates
- Audit logging, detection, and security-focused monitoring
These are the highest-priority weaknesses because they sit directly on the boundary
between the intended role model and the real attack surface. They represent the
difference between good architectural intent and a launch-ready defensive posture.
Hardening direction
The hardening path is to put Cloudflare edge protection in front of the public
surface, enforce strict role boundaries inside the API, keep internal services
private, add GitLab security gates to delivery, and feed security telemetry into the
monitoring stack.
That gives ValkenRoot a practical launch-ready baseline while preserving the longer
path toward richer world systems, operations tooling, and governance layers.
The emphasis is on realistic hardening rather than overbuilding: secure the edge,
secure the roles, secure the pipeline, secure the internal services, and make abuse
visible enough that the team can respond early.